Santa Claus is an elderly business owner, resident of the North Pole. His business involves receiving the Christmas wish lists of millions of children across the world during the month of December, organising the manufacturing and acquisition of all the toys, and then, delivering the presents to every child worldwide on the night of Christmas Eve. To perform the mammoth deliver job, he uses a large sleigh and a team of 9 reindeer that can run across the sky.
In recent years, Santa has embarked upon a digital transformation, adopting Artificial Intelligence to predict wish lists, using the cloud to store children’s personal data and adopting a security culture within his workshops. Santa is proud of the steps he has taken towards modernizing his organisation and spoke to us about the cyber security he has embraced to support these changes.
1. What made you transition your legendary organisation into the modern digital world with the very latest technology and processes?
I’m not embarrassed to tell you that it was me being stuck in the past, caught up with tradition and reluctant to change, that almost caused my own extinction. These days, if you do not exist online, then you do not exist. This refusal to update my brand to the current day was slowly demolishing the already waning Christmas spirit. If children stop believing in Santa Claus, then the magic dies and I no longer have a job. This belief was getting lower each year, until in 2015, my sleigh could no longer fly. The reindeer had to run on the ground for much of the night and many children went without presents, my reputation was almost ruined.
I made a decision that night, that I was going to get over my barrier to tech, break down that wall and get myself online with every other modern business. I employed the very best CTO I could find, Ms Holly Berry, and we have transformed the organisation inside and out. In memory of that tough night, my reindeer have renamed themselves:
- Device
- Patcher
- Virus
- Phisher
- Cloud
- Browser
- Ransom
- Asset
- Host
- Router the red nosed reindeer
2. Staff awareness and training
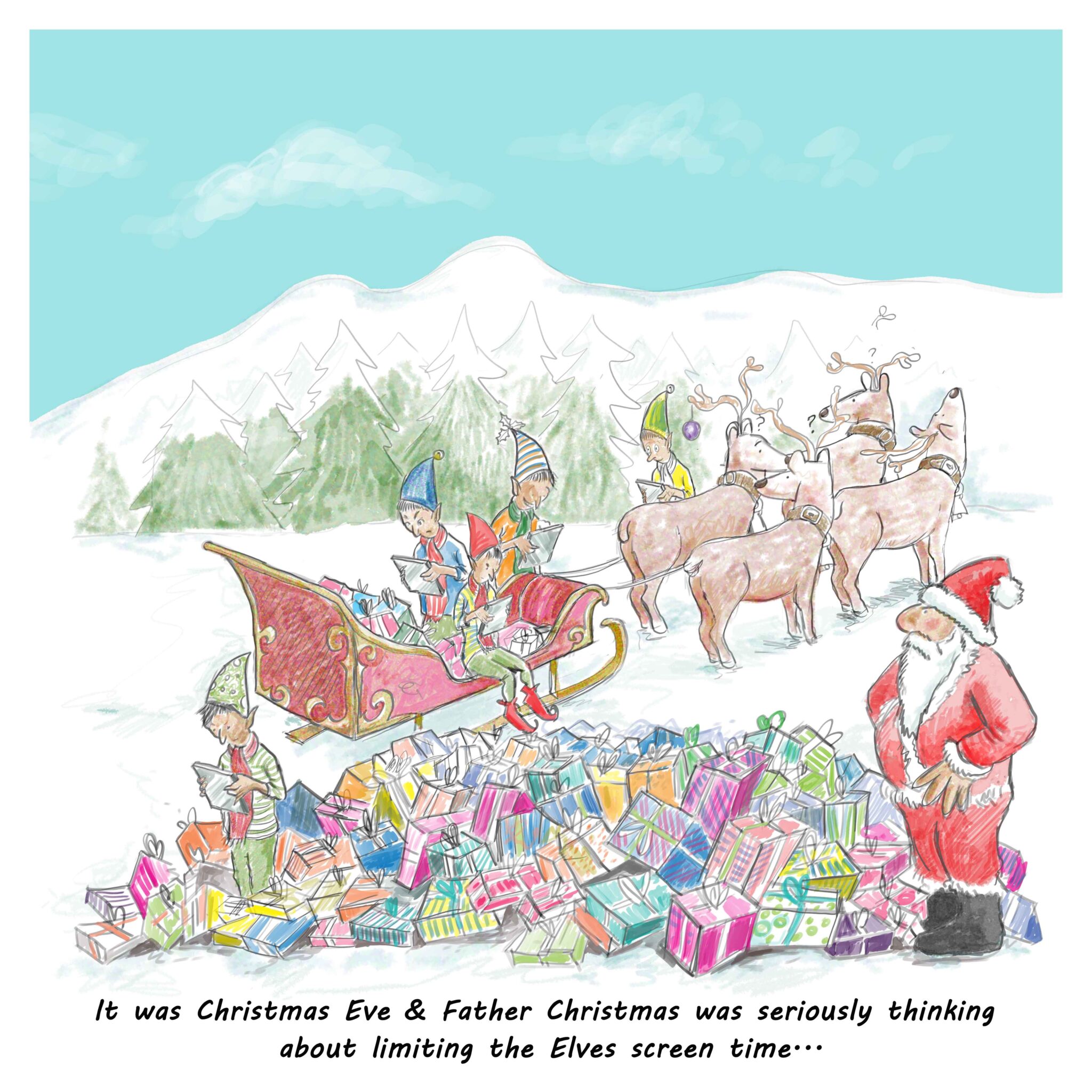
The Elves are one of the pillars of the business, and I cannot deliver the Christmas magic without them. When we went digital and started operating fully online, I needed their cooperation and support, so training was crucial. Now, they are all kitted out with secure company laptops, user accounts, secure passwords and 2FA. Recognising that 10 out of 10 Elves chose Elf1234 as their password, was a learning milestone for the workshop, as was the lesson of not sharing passwords or accounts. This went against the grain for elves as many of them are related and like to share. We also need weekly updates on the latest phishing threats as they can be rather naïve in this area. As an organisation, we are particularly on the look out for a Narwal attack (this is a very serious targeted attack intended to bring down Christmas).
3. Who would attack Santa Claus?
It is a good question, and it may come as a surprise to hear that not everyone loves Christmas. One example is that festive killjoy, the Grinch who tries to spoil Christmas each year. It is fortuitous that due to his long pointy fingers, he never really got into tech in a big way and thus his potential damage to Christmas is limited.
As you know, there are no financial transactions within the North Pole operations, but we do hold an awful lot of information, and it is information that naughty people could sell for a lot of money. Our data is almost exclusively about children, their wishes, their habits, their history and their addresses. This is highly sensitive and for that reason it is all encrypted at rest and held in extremely secure private cloud storage. Those of my little helpers that are authorised to access this data are highly controlled and we have many processes and procedures in place to limit this.
Last year my organisation certified with Cyber Essentials and this now gives us peace of mind that we have the key controls in place to protect us from most cyber attacks. It additionally reassures those in our supply chain who also deal with confidential information, #Toothfairiesarereal, #Easterbunnydoesitbetter, #Frostythesnowmaniscool.
4. What are the security issues that you are worried about for the future?
My sack is increasingly filled with smart devices, things that connect to the internet. I’m not just talking about speakers and fitbits, no, things like talking dolls and teddy bears that ‘listen’ to the child and respond. My worry is that the device is unsecured and a third party could interact with the child, listen, take pictures, or track the child through the toy if they were in range. These internet connected toys raise security and privacy issues and I’d recommend that the parents find out what security measures are in place before allowing their children to play.
Santa’s secure check list for smart devices:
- Does the device have a default username and password? Change these, use unique complex passwords and 2FA if possible.
- If the device has a hard coded password, do not use it.
- Have you changed the default password on your home router?
Merry Christmas from IASME!